According to studies carried out already in 2017 by the German Association for Information Technology, Telecommunications and New Media (Bitkom), for example, no less than every second company in Germany has been affected by data theft, industrial espionage, or sabotage within a 2-year period. Presumably the actual figure is even much higher. Annual losses are now likely to be in the upper double digits of billions.
However, despite these alarming figures, most public attention is concentrated predominantly on attacks on critical infrastructures, governmental institutions, or malware infections on a global scale, reminiscent of the "WannaCry" blackmail software, which caused quite a furor in 2017. This software encrypts data which can only be recovered decoded – if at all – by paying a ransom in Bitcoins. This also demonstrated that industrial and production systems were now equally at risk as classic IT systems. Whether IT or OT has long since been irrelevant to malware and hacker attacks.
"WannaCry" also showed us something else. Namely that there is still a tremendous backlog for OT regarding cyber security. Even though effective security updates and patches to combat this malware have been available for many years now, the problem continues to persist in this environment. While processes to close gaps in security as quickly as possible were established for IT systems long ago, it seems that this has not likewise been a matter of course for OT, and protection measures are implemented only selectively. The potential for loss in industry should certainly not be any less of a consideration.
But where can the reasons for this apparent discrepancy be found? One reason may simply be down to history, as the issue of security for OT is a lot more recent than for IT. The life cycles of automation components and systems are also a lot longer than those for IT systems. "Security by Design" approaches were only really considered with any resoluteness for the latest generation of automation systems.
New methods of attack
Risks have been steadily increasing over the last few years and new threats are emerging all the time, posing a particular threat to the existence of small companies: Blackmail using ransomware. Unlike with industrial espionage where hackers gain access to corporate networks to harvest data for as long as possible without detection, data in ransomware attacks is encrypted and therefore rendered unusable.
These attacks are easier to execute and are less target-oriented than with espionage. The malware is sent out indiscriminately and the hackers then attempt to extort a ransom with comparatively low demands. These kinds of attacks are nevertheless extremely dangerous for companies, as blocking of the system takes effect throughout the entire company. Nothing works any more. No more access to customer or logistics data and a complete block on access to machines, programs, applications or systems as all data is encrypted and has thus been rendered unusable.
If the company has made the error of allowing back-up systems to also be accessed through the networks, these are encrypted first causing maximum damage. Even if the ransom is paid there is no guarantee that the decryption code will be handed over, or that it will actually work. In many cases, the blackmail does not stop there. The BSI (German Federal Office for Information Security) therefore recommends that no payments should be made.
However, the capabilities of cyber attackers and their options are also constantly evolving. It is to their benefit that the trend in digitalization is providing ever progressive networking and increasing volumes of data. Effectively, networking makes it easier for attackers to access data or components, and data is even being referred to as the "new oil" or also the "new gold". Despite misleading comparisons, data is driving digitized industry forward and is becoming ever more valuable. As a result, cyber criminality is becoming easier, and at the same time more lucrative. A veritable "gold rush" in the world of cyber criminality can be noted.
Defence against cyber attacks
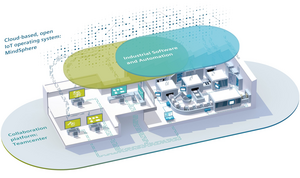
There are now proven and effective concepts which are tailor-made for the necessities and requirements of OT to defend against cyber attacks. Siemens strongly recommends a multi-layer defence concept which covers all levels in this regard, i.e. according to the "Defence-in-Depth" principle.
A multi-layer defence combines an array of security measures covering plant security, network security, and system integrity. In addition to technical measures, organizational measures such as guidelines and processes, as well as the monitoring of automation systems for anomalies are incorporated as protection for the overall system, ensuring that any attack is discovered as quickly as possible and major losses can be avoided. Network security includes all measures to inhibit unauthorized access to automation networks and eavesdropping or falsification of industrial communication, such as firewalls or the use of encrypted protocols. Finally, system integrity includes all elements for the protection of automation systems and terminal devices, such as controllers, industrial PCs and SCADA systems with integrated security mechanisms.
The benefits are clear: The time and effort required by hackers to bypass multiple defence levels that are all synchronized with one another is immense. At the same time, yet another problem is solved: vulnerabilities in software and products. Constant security updates show that such vulnerabilities will never be entirely prevented. A certain amount of time is also required from initial identification to provision of the patches, and ultimately actual elimination for the user.
The Defence-in-Depth concept ensures that individual vulnerabilities cannot be exploited, or that any exploitation does not result in losses as alternative security measures continue to provide effective protection. Should hackers succeed in gaining access to the network, they still will not be able to access the terminal devices. Conversely, vulnerabilities in terminal devices cannot be exploited if the hacker does not have access to the network. Needless to say, inside perpetrators represent a particular challenge here, however, special measures such as physical access checks and the 4-eyes principle, etc. can be introduced in a remedial capacity.
Crisis or opportunity?
Cyber security for industry, Industrial Security for short, is and remains a challenge. However, that is not to say that it cannot be resolved. As long as the manufacturers of industrial automation, network and software components ensure that the security characteristics and functions adapt to an ever increasing threat, and furthermore ensure that this is maintained with corresponding services during operation, even machine manufacturers and operating companies of industrial systems can protect their assets to a reasonable degree and utilize the benefits of digitalization unscathed.
Franz Köbinger, Marketing Manager Industrial Security at Siemens AG