Futurism Technologies. As businesses continue to adopt coming-of-age hybrid cloud and storage environments, IT ecosystems too have evolved from old school and perimeter-based monolithic IT structures to more intricate multi-cloud and perimeter-free environments. These complex yet advanced IT ecosystems disperse connected devices, data and users across a gigantic network of workloads and applications.
With organizations responding to new social and business dynamics embracing new technologies, the need for next-gen and future-proof security approach was never this evident. IT security has always been based on perimeter defense framework, like the walled cities and fenced castles of the Middle Ages. The idea is to keep intruders at bay while assuming full trust on the ones inside the walls to roam freely. Unfortunately, the perimeter security concept has been under siege for several years now, thanks to the inflating networks of connected devices and mass adoption of remote work concept.
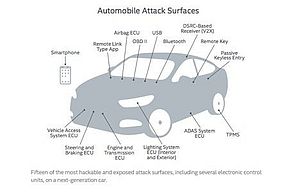
As organizations get aboard the digital transformation wave while the diversity of security continues to inflate, new security models like Zero Trust are proving out as a boon in helping bring context and insight into the rapidly exploding attack surface. Businesses today need a security framework that is uncompromised and offers protection against new and coming-of-age threats including new strands of Ransomware, multi-prong attack tactics and social engineering hacks.
Lack of Security Intel
With remote work becoming the new normal, an increasing number of organizations are resorting to the Internet of Things or IoT. According to the State of the Network Study report, more than 50% of IT experts had deployed IoT devices in 2021 owing to a range of benefits that these devices offer. For example, they help manufacturing companies monitor the performance and efficiency of industrial processes without the need of having the staff on site. These devices also provide health care personnel a means to track vital signs of patients in hospital or at home from a remote location.
Unfortunately, most organizations lack critical security insights into these connected devices. Part of the problem might be the startling fact that there’s no one at the site to manage these devices. With more and more people working remotely, employers are paying less heed to their connected devices. Therefore, failing to monitor them for potential malware infections, security vulnerabilities and other security issues.
5 Reasons Businesses Need to Wake Up To the Idea of Zero Trust Security
1. How secure are your cloud-based business initiatives?
Last few years have witnessed a massive surge in the number of organizations jumping into the hybrid cloud ecosystem. Though hybrid and multi-cloud help an organization grow, compete effectively and transform operations, these benefits require a modernized and reimagined focus when we talk about enterprise security.
Zero Trust security acceleration services help to protect all your multi-cloud and hybrid cloud investments, bringing in a new and balanced set of policies, governance, configurations, controls and automation across users, data and diverse cloud workloads. It brings visibility and context helping to maximize compliance while improving monitoring and reporting.
Zero Trust helps to achieve improved security and maturity model. It helps security professionals and IT teams follow a use case based framework to help mature existing or new security capabilities.
2. How strong is your data privacy control strategy?
Nothing is more important to a brand’s reputation than keeping its customer data safe and confidential. Ensuring optimum data privacy is quintessential to build brand loyalty and trust. With businesses working in diverse and distributed ecosystems these days, security unarguably is the key focus.
Zero Trust assumes a no trust policy wherein every user, every connection and every device is verified rigorously. It helps to preserve customer data privacy, drive transparency and accountability across the organization with intelligent and risk-based authentication.
Zero Trust paves way for a proactive security approach helping businesses rethink their idea of data security while helping them meet data privacy requirements and regulations. Organizations can define a multi-disciplinary and strongly integrated security strategy using a Zero Trust framework.
3. How do you control access to customer data in your organization?
Protecting your customer data is essential for one big reason: your business relies on it.
With the number of attacks increasing at lightning speed with no signs of slowing down, protecting customer data is more important than before.
Zero Trust IAM (Identity & Access Management) approach provides a powerful and modular IAM approach that leverages context and data –driven insights and analytics to decide who will get access to what and what they will do with it through a strong and intelligent multi-factor and risk-based authentication powered by Artificial Intelligence (AI).
Zero Trust IAM offers:
• Mobile multi-factor authentication and risk-based access policies driven by AI
• Powerful control over digital identities and assets with identity federation
• Sound balance between security and usability
• Smarter and intelligent hybrid IAM approach
4. How good are you when it comes to detecting and tracking credential stuffing?
Credential stuffing is one of the most disturbing security vulnerabilities wherein hackers target networks of web infrastructure and breach into a user’s accounts using stolen credentials. This not only harms a brand affecting its revenue, but also affects customer trust.
Employees’ business accounts are doorways to an enterprise’s data chamber and employee credentials are the keys to these chambers. Unfortunately, humans aren’t that good in keeping the keys to these chambers safe thus, leaving the doors of chambers wide open for attackers.
Did you know?
According to FBI Security Advisory, hackers leveraged bulk loads of credentials to carry out fraudulent check withdrawals and ACH transfers amounting to a whopping $3.5 million from a renowned financial organization.
Attackers unleash thousands of bots to execute commands to steal millions of customer data. This is the reason organizations need extra protection to keep identity and privileged access breaches and attacks at bay.
5. How do you secure and monitor a remote worker’s access to your IT systems and networks?
As more and more companies adopt the remote work concept, employees are accessing mission-critical business data, networks, applications and other sensitive data from disparate sources, devices and networks. This has opened the doors to new security challenges, threats and vulnerabilities.
Zero Trust security helps an organization to better position itself to prevent breaches and attacks that may include stolen credentials, user impersonation, password reuse, credential stuffing, etc. Implementing a Zero Trust security approach can help businesses eliminate the standard and old school password protection method, which is a common cause of phishing attacks.
Zero Trust can protect the dispersed remote work ecosystem with real-time insights and threat intelligence.
Takeaway
Zero Trust security paves the way for a proactive security architecture helping businesses to reimagine their approach to securing data. Old school incident respond techniques and approaches often leave IT and security teams perplexed and overwhelmed when it comes to detect and prevent sophisticated attacks.
Zero Trust can easily adapt to the complex modern security and IT infrastructure, embrace hybrid and multi –cloud environment and protect data, devices, apps and people irrespective of where it stays or goes.
It helps businesses to simplify risk management by eradicating implicit trust concept. Irrespective of the situation, user, access method and user location, security takes a center seat with the most extreme, proven and tested security checks.